
How to Read DMARC Aggregate Reports
DMARC aggregate reports are packed with useful data but arrive as unreadable XML. Here is how to parse them, what to look for, and how to build a monitoring routine.

DMARC aggregate reports are packed with useful data but arrive as unreadable XML. Here is how to parse them, what to look for, and how to build a monitoring routine.

DMARC aggregate reports are packed with useful data but arrive as unreadable XML. Here is how to parse them, what to look for, and how to build a monitoring routine.
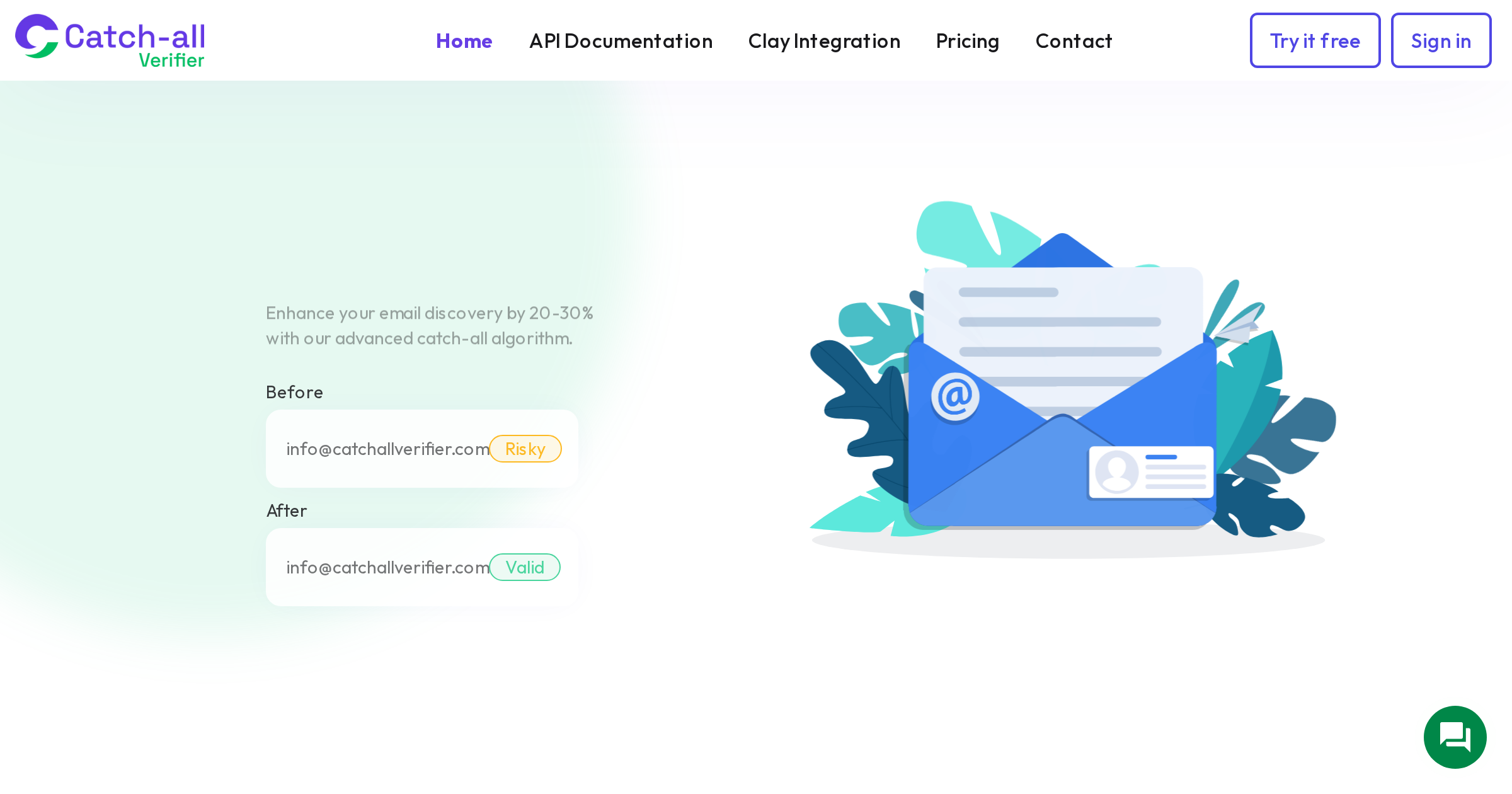
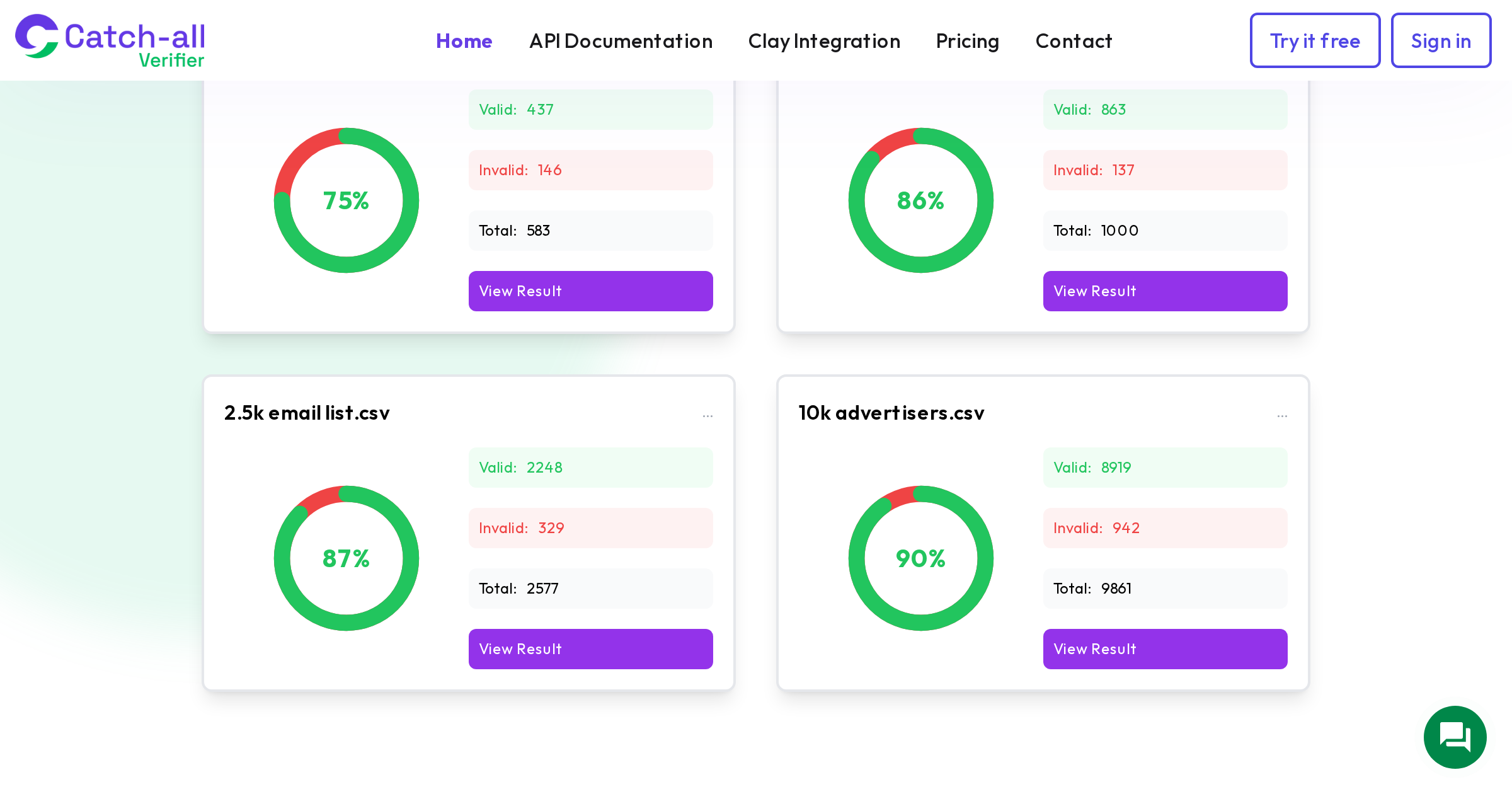
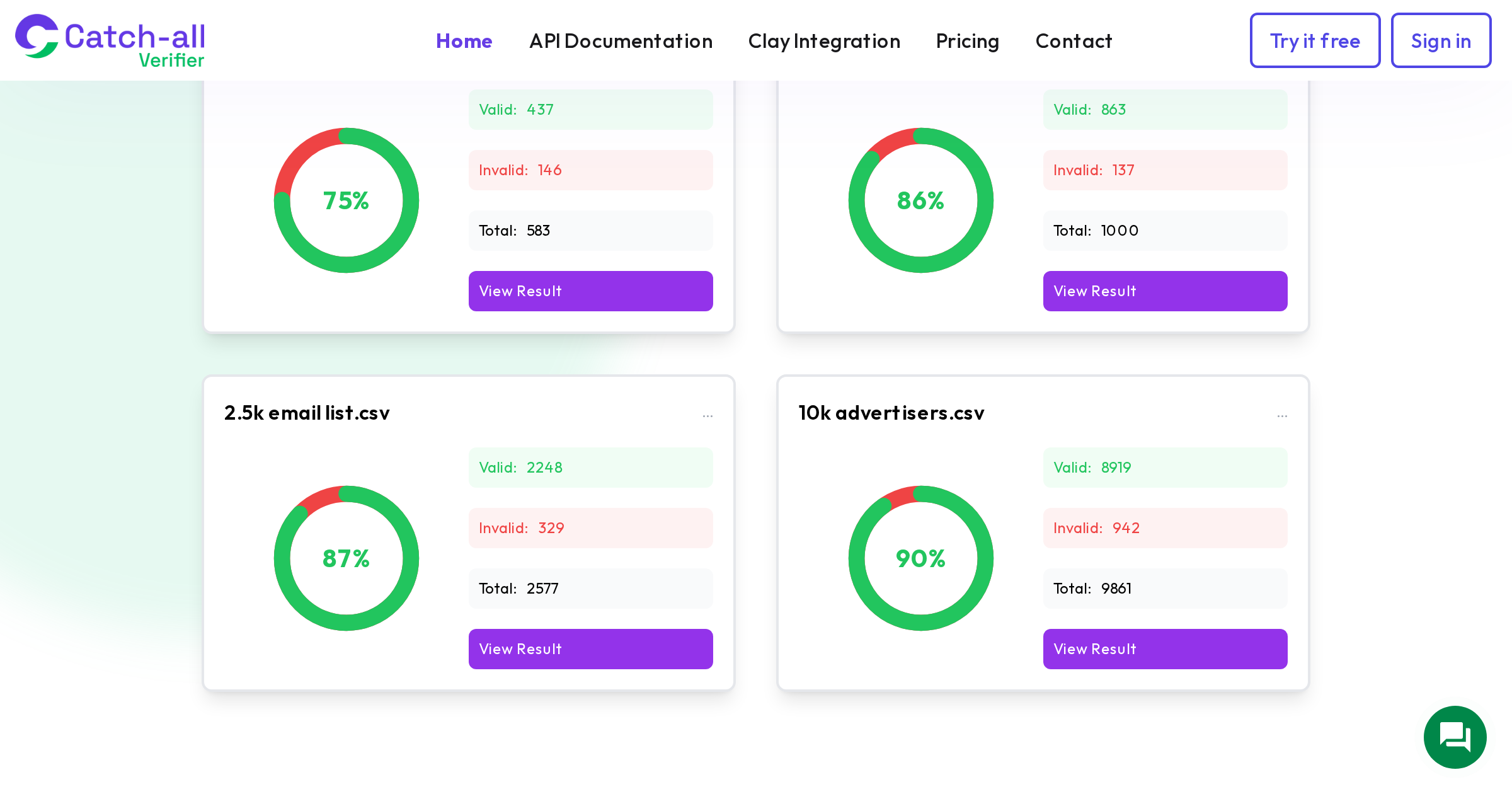
Only 62% of all submitted email addresses are valid upon verification. If you have never audited your email database, there is a good chance a quarter or more of your contacts are dragging down your deliverability. Here is how to run a proper audit.
Managing SPF, DKIM, and DMARC across Google Workspace, Mailchimp, Salesforce, and cold email tools simultaneously without breaking the 10-lookup limit or failing DMARC alignment.
Salesforce-specific guide for implementing email verification within lead management workflows using Flow and API integration.
Most cold email A/B tests produce garbage results because of small samples and sloppy design. Here is a framework for tests that actually produce reliable insights.

Marketing agencies need standardized verification across all client accounts to prevent cross-contamination of sending reputation. Learn workflows, cost management, and reporting strategies.
Open rates are broken thanks to Apple Mail pixel pre-loading. Here are the deliverability metrics that actually tell you what is happening with your emails in 2026.

Higher education domains show 40-60% catch-all rates. Learn verification strategies for enrollment marketing, faculty outreach, alumni fundraising, and EdTech sales to universities and K-12 schools.
Email deliverability varies dramatically by country due to different regulations, dominant providers, and cultural norms. Here is a practical guide covering the US, Germany, Japan, Canada, and other key markets.
Most sales teams have no idea what a meeting through cold email actually costs. Here is the full calculation including infrastructure, tools, verification, and team time.
HubSpot-specific integration using workflows, APIs, and Zapier for automated email verification of new contacts.

Most organizations set DMARC to p=none and stop. Here is the step-by-step process for progressing to p=reject with percentage ramps and monitoring at each stage.
50 articles total